Stategraph integration for Terrateam. Run Terraform plans in parallel without the global state lock.
Run Terraform in pull requests without the constraints
GitOps automation that adapts to your workflows, not the other way around. Plan, govern, and ship on your terms.
Works with your favorite tools
Open Source
Infrastructure changes, right in your pull requests
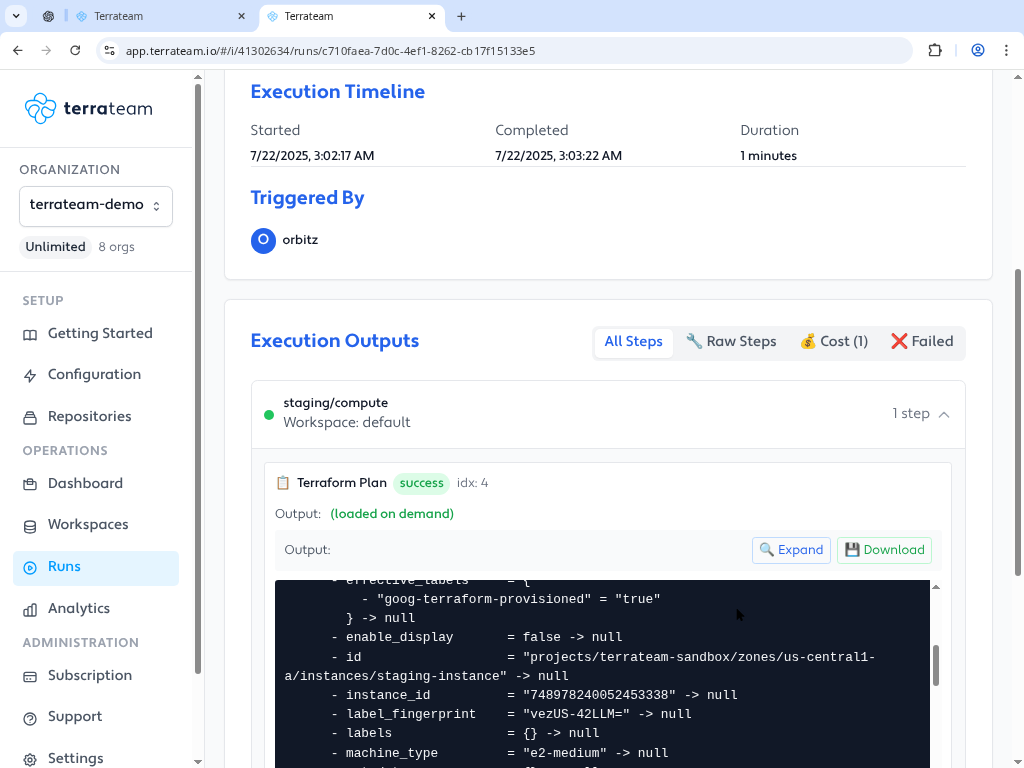
Terrateam gives you complete visibility into every change before it hits production
Expand for plan output details
+ google_compute_instance.api_servern2-standard-4 instance in us-central1-a
+ google_compute_disk.data500GB SSD persistent disk
Plan: 2 to add, 0 to change, 0 to destroy
Cost Estimation
Expand for cost estimation details
| Dir | Workspace | Previous (USD) | New (USD) | Diff (USD) |
|---|---|---|---|---|
| production/compute | default | 1,847.32 | 2,113.56 | 266.24 |
| Total | 1,847.32 | 2,113.56 | 266.24 | |
Approval Requirements
To apply all these changes, comment:
terrateam applyTrusted by teams balancing security, compliance & speed
Your workflows, your rules
Terrateam is aggressively unopinionated. Whether your repo structure is pristine or chaotic, your workflows conventional or custom, we won't try to fix you. We'll hand you a bigger lever.
Works with any engine
Terraform, OpenTofu, CDKTF, Pulumi, Terragrunt. Use any IaC tool with the same workflow.
Read the documentationCost estimates in every PR
See the financial impact of changes before they're deployed with built-in cost estimation.
Learn about cost estimationDirectory-level RBAC
Fine-grained access control with policy override approvals for exceptions when needed.
Explore access controlsMonorepo support
Parallel runs, drift detection, and caching for complex repositories with multiple environments.
Monorepo best practicesDeploy anywhere
Self-host or use our single-tenant cloud offering. You control where your data lives.
Deployment guidePull request-native workflows
Works directly in your existing workflow with pull requests, comments, and approvals.
How it worksSee the full impact of every change
Terrateam gives you a clear, structured GitOps workflow so you can plan, validate, and deploy infrastructure changes with complete confidence.
Propose Changes with Full Context
Push infrastructure changes to a pull request, Terrateam kicks off everything from there. Works with Terraform, OpenTofu, Pulumi, CDKTF, and more.
resource "aws_eks_cluster" "main" {
name = "data-processing"
role_arn = aws_iam_role.eks.arn
version = "1.24"
}Validate Plans, Policies, and Costs Instantly
Terrateam runs every check: what changes, what it costs, and whether it’s compliant. All inside your pull request, before anything hits production.
The Right People Approve Every Change
Terrateam enforces approvals based on your team structure and security rules, no changes can bypass required review.
Apply with Confidence
Once approved, Terrateam applies your changes safely, with locking, logging, and full auditability built in.
Discover the full power of GitOps orchestration
Terrateam's orchestration engine brings structure, security, and speed to your infrastructure workflows. Learn how it can transform your team's productivity.
Orchestrated runs with dependency awareness
Policy-based workflow routing
Policy enforcement with override capabilities
# .terrateam/config.yml
# Apply policies to enforce team-based gatekeeping
apply_requirements:
checks:
- tag_query: "dir:environments/production/**"
approved:
enabled: true
any_of: ["team:platform"]
- tag_query: "iam in dir"
approved:
enabled: true
all_of: ["team:security"]
# Enable cost estimation in PRs
cost_estimation:
enabled: true
currency: "USD"
# Custom workflow with policy enforcement
workflows:
- tag_query: "dir:environments/production/**"
plan:
- type: init
- type: plan
- type: conftestInfrastructure that scales with your team
IaC at Scale
Manage thousands of resources across teams with automated workflows and policy enforcement.
Governance & Security
Implement automated governance and secure collaboration with policy enforcement and audit trails.
Developer Self-Service
Empower developers to provision and modify infrastructure through self-service workflows with built-in guardrails.
Real results, measurable impact
"Terrateam made it a lot easier for me and others to make Terraform changes and stay aligned."

"I’ve been totally removed from the loop. Developers can now deploy on their own."

"Terrateam helps us enforce the separation of duties required for SOC 2."

Zip
How Zip enabled 130+ engineers to confidently manage infrastructure with a security-led GitOps rollout using Terrateam.
Why companies love Terrateam
Powerful GitOps tooling without the complexity
Infrastructure orchestration that fits your workflow
Terrateam brings GitOps, policy, and automation to your infrastructure stack.
Get started for free, no credit card required.