Secrets and variables
Terrateam provides several ways to manage sensitive information and customize your Terraform configurations using secrets, variables, and tfvars files. This guide will walk you through how to create and use secrets, set environment variables, and use tfvars files to manage your Terraform variables.
Secrets
GitHub Secrets can be used to store sensitive information. They are translated into environment variables in the Terrateam GitHub Action runtime environment. These environment variables may be referenced in your Terraform code.
TF_VAR environment variables
Secrets that start with TF_VAR_ are treated specially by Terrateam. GitHub Secrets are always uppercase, however by convention Terraform variables are lowercase. Terrateam automatically finds all secrets that start with TF_VAR_ and creates a new environment variable that has the lowercase name. If the lowercase name exists, no action is taken. The uppercase environment variable is left unchanged. For example, the secret TF_VAR_LOGIN_TOKEN will create a new environment variable called TF_VAR_login_token.
Creating secrets
Prerequisites
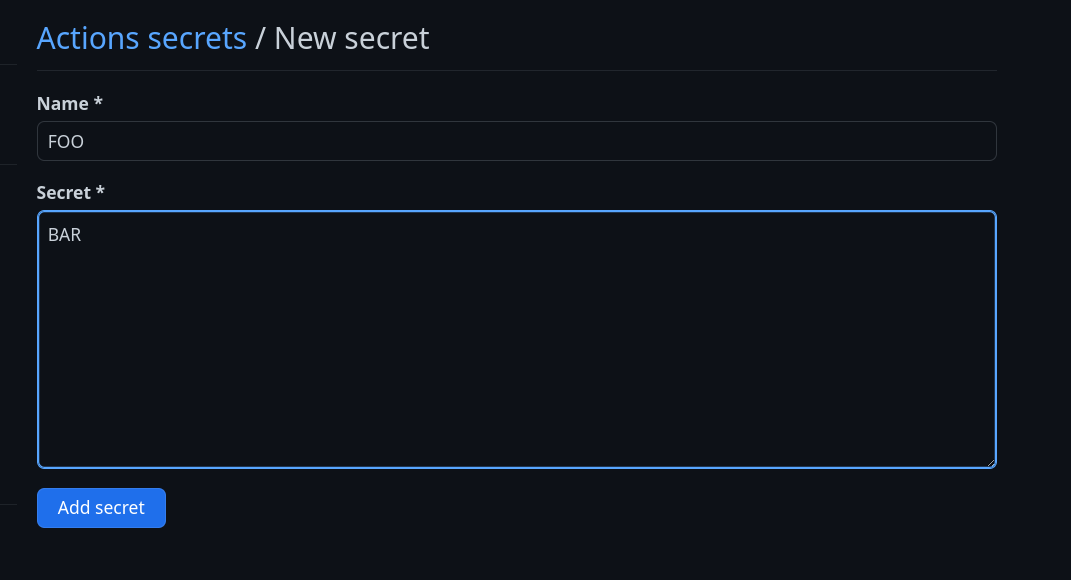
Create a new secret
- Export your Terraform
organization/repocombination as an environment variable.
export REPO="OWNER/REPO"- Create a new repository secret
gh secret --repo "$REPO" set SECRET_NAME- Navigate to the main page of your Terraform repository on GitHub
- Select
Settings
- In the left sidebar, select
Secrets → Actions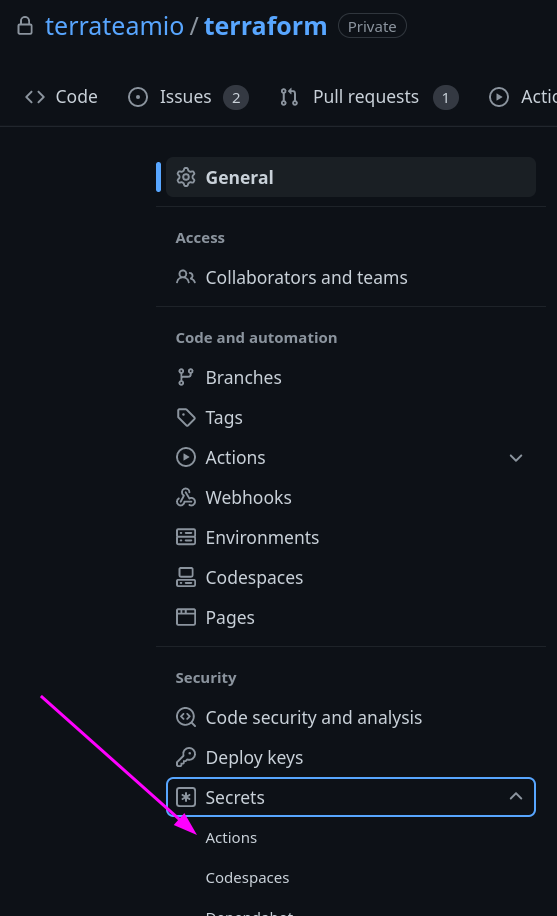
- Select
New repository secret
- Add your new secret
Environment variables
Terrateam allows you to set environment variables using hooks and workflows.
Hooks
You can set an environment variable at the very start of a Terrateam operation using hooks.
hooks: plan: pre: - type: env name: FOO cmd: ['echo', 'BAR'] post: [] apply: pre: - type: env name: BAZ cmd: ['echo', 'QUX'] post: []Workflows
You can also set an environment variable at the start of each plan and apply operation workflow execution.
workflows: - tag_query: "" plan: - type: init - type: env name: FOO cmd: ["echo", "BAR"] - type: plan apply: - type: init - type: env name: FOO cmd: ["echo", "BAR"] - type: applytfvars files
Terraform allows you to define variables in .tfvars files, which can be used to customize your Terraform configurations. Terrateam supports using tfvars files to manage your Terraform variables.
Using tfvars files
To use a tfvars file with Terrateam, you can specify the file path in your workflow configuration using the extra_args option.
workflows: - tag_query: "" plan: - type: init - type: plan extra_args: ["-var-file=qa.tfvars"] apply: - type: init - type: applyIn this example, the qa.tfvars file will be used during the plan step.
